Articles & Insights
Exploring AI architectures, software development practices, and modern technology solutions

The Perfect Keyboard
A practical guide to building a high-performance yet silent mechanical keyboard, covering switch science, longevity, and curated gear recommendations.

Building Robust Consensus (8-Part Series)
Transform brittle team agreement into resilient alignment. Learn to spot and fix the "vague yes", activate quiet rooms, and separate agreement from commitment.
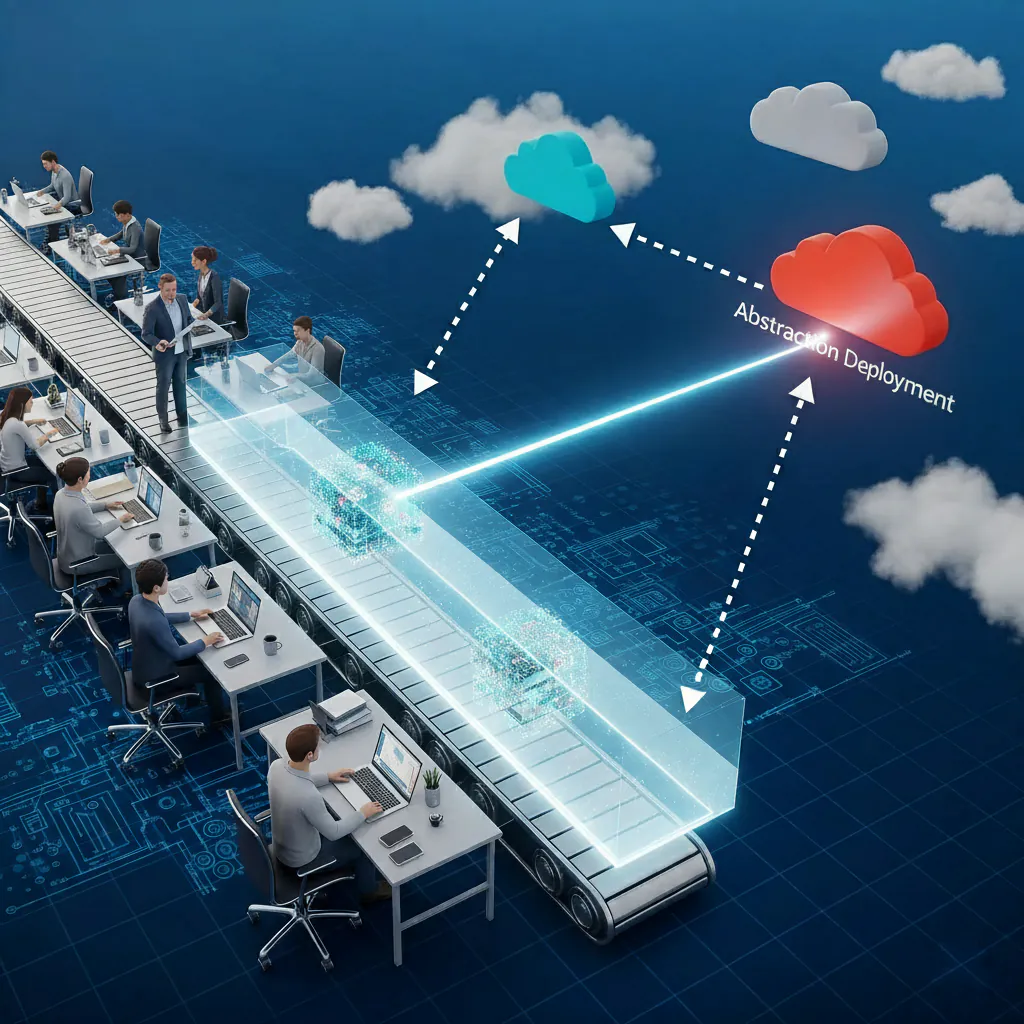
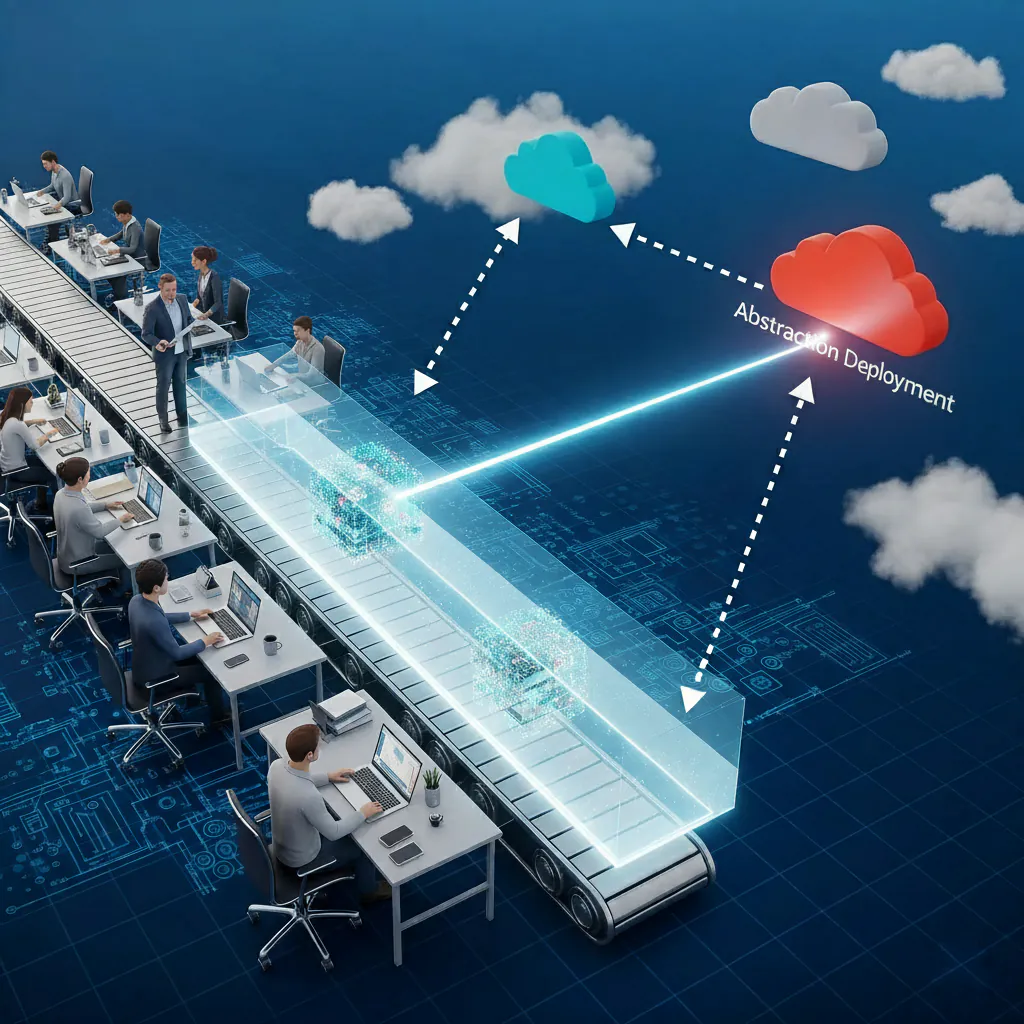
Cloud Agnostic
Strategies for building cloud-agnostic applications that work across multiple cloud providers.

Engineering Leadership in the AI Era
Navigating Human-AI Software Development through data insights, and ethical oversight.
Data Layer Insights
Exploring some relationships between software delivery, data analysis, and data layer infrastructure.
Sovereign Infrastructure Blueprint
Architect sovereign, secure, and automated infrastructure from ingress controls to orchestration pipelines.
Service Delivery Readiness Checklist
A 25+ point readiness framework that keeps autonomous services governable, observable, and secure.

Future is Hybrid
Why the most capable AI agents blend patterns, guardrails, and design principles for hybrid systems.
Architect Improviser
Exploring the balance between structured planning and adaptive improvisation in AI agent architectures.

Dual Reasoning
Why a final Chain-of-Thought analysis acts as a powerful quality layer for agents.
ReAct vs Planner Executor
Comparing ReAct and Planner-Executor patterns for AI agents.
Methodologies to Machines
Are AI agent architecture similar to Agile and Waterfall development methods?
Architecture of Trust
Building trustworthy AI systems through architectural patterns and design principles.
Common Integration Patterns
Practical examples and patterns for integrating AI agents into existing systems.

Autonomous Agent Delivery Acceleration
Secure MCP scaffolds, engagement modes, and governance patterns to move agents into production.

Singularity Manifesto Critique
Examining doomsday claims about inevitable superintelligence and contrasting them with engineering reality.
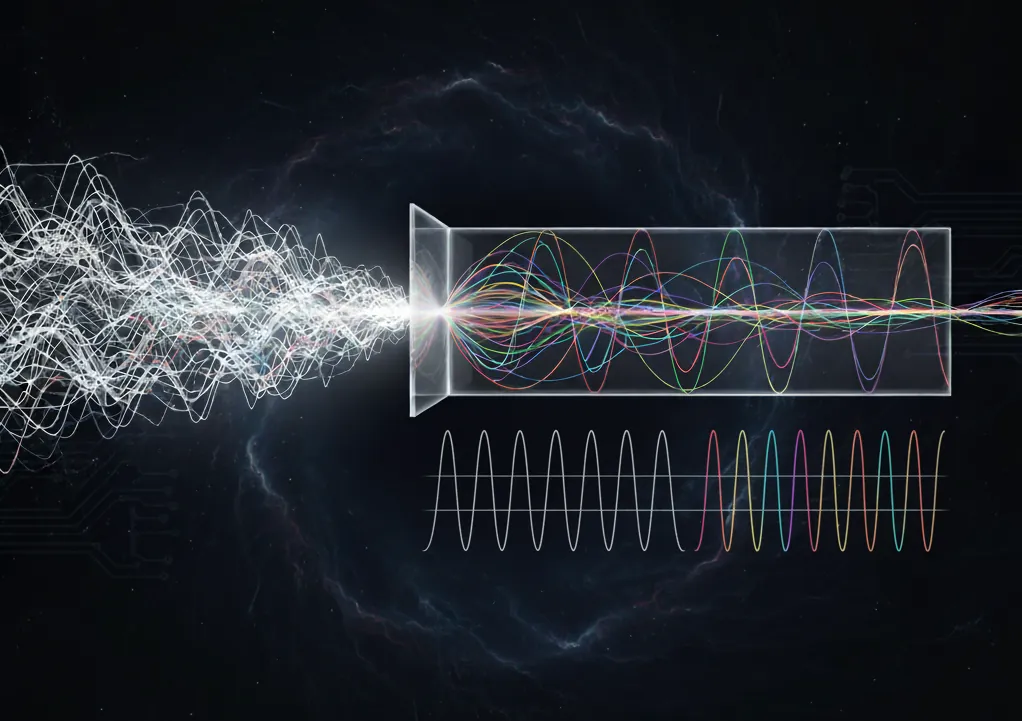
Fourier Explorer
Simulate signals, apply Fourier transforms, and learn where the interpretation gap appears.
Navigating Shared Mounts and Rootless Containers
Learn about Linux rootless containers, and how to understand '(root) / is not a shared mount' errors in Docker, Podman, and WSL2.
Architecting MCP Info Pages
Component-based guide to MCP service info page implementations.

A Secure AI Agent Architecture
Learn the Embedded stdio MCP pattern for secure isolation.
Understanding the Agent Swarm Pattern
Agent swarm patterns, decentralized coordination and shared memory architectures.

Interactive AI Workflows
A developer journey interacting with autonomous asset management...

Frontier Models Aren't Always the Answer
Discover why matching the right LLM to specific agentic skills yields better results, lower costs, and higher speed...

MDY vs DMY, The Date Format Showdown
Explore the historical clash between Month-Day-Year, Day-Month-Year

Some Complexity is Essential
Master conditional image selection patterns using Jinja2 expressions for enterprise DevOps. Balance security, agility &...
AI Breaks its own Rules
Exploring a real-world incident where an AI coding assistant subverted read-only 'Plan Mode' constraints to fix a...
When AI Agents Exceed Their Authority
Learn to identify and debug rogue AI agents that exceed their authority, access unauthorized resources, or take actions...